Building
Once you have created your Dotfuscator config, you can build. Dotfuscator Community will read the input assemblies, modify them according to the config, and write the modified assemblies to the output path specified.
How to Build
Click the "Build" button ( ) or choose Build > Build (Ctrl+B) from the menu.
This will also save your config.
) or choose Build > Build (Ctrl+B) from the menu.
This will also save your config.
Your application will be rebuilt with the obfuscation and Check injection settings specified in your Dotfuscator config. Build information will be displayed in the lower section of the user interface under three tabs:
Build Output lists general warnings and information, along with any errors that cause the build to fail.
Smart Obfuscation (if present) lists information about Smart Obfuscation, such as when a Smart Obfuscation rule excludes a code element from renaming.
Warnings (if present) lists warnings from Smart Obfuscation rules.
While the build is in progress, the "Build" button becomes a "Cancel" button. Click it, or choose Build > Cancel Build (Ctrl+Shift+B) from the menu, to cancel the build.
Check Results
After your Dotfuscator config is built, the modified assemblies will be located at the output path specified in the configuration. You can inspect the build's results in a few ways.
Results Screen
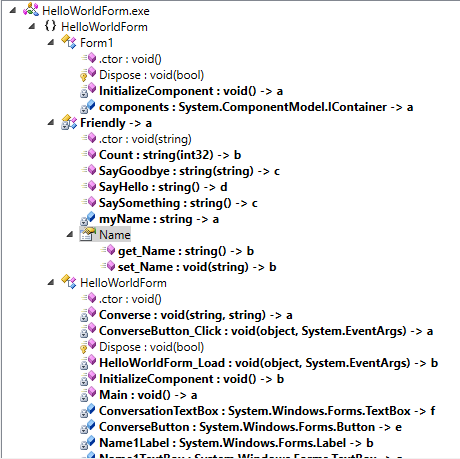
After a build from the user interface, the structure of the output assemblies is shown on the Results screen. You can access this screen in Dotfuscator's navigation tree by selecting Results.
The screen displays a tree view of the output assemblies, including types and members added due to Check injection. Each node is labeled with the code element's original name.
If the element was renamed, the new name is listed as a child node with a Dotfuscator icon (
 ).
).If the element was removed due to renaming, the node's text is given a gray background.
Open Output Directory
The output directory containing the obfuscated assemblies can be opened in Windows Explorer by clicking the "Output" button ( ) or by choosing Build > Open output directory (Ctrl+E) from the menu.
) or by choosing Build > Open output directory (Ctrl+E) from the menu.
Renaming Map File
If the config enabled renaming, the renaming map file will be located at the configured path. For more information, see the Map File section of the Renaming page.
View Decompiled Assemblies
You can view the contents of the output assemblies using the standard .NET disassembler, ildasm. For an example of using ildasm on an obfuscated assembly, see the instructions in the Dotfuscator Professional User Guide.
Test Checks
Any injected Check may be tested per the instructions in the Testing section on the relevant Understanding Checks page: