Like any other development project, app protection initiatives are at the mercy of scope, time, and bandwidth for ongoing support. That’s why it pays dividends to have protection programs that are easy to implement.
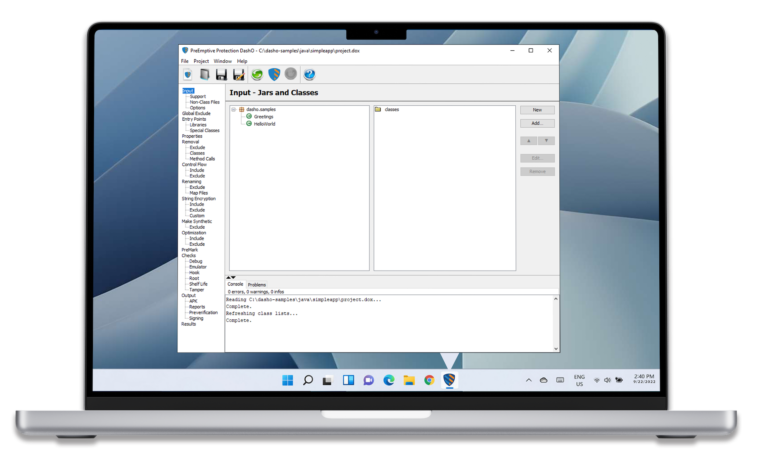
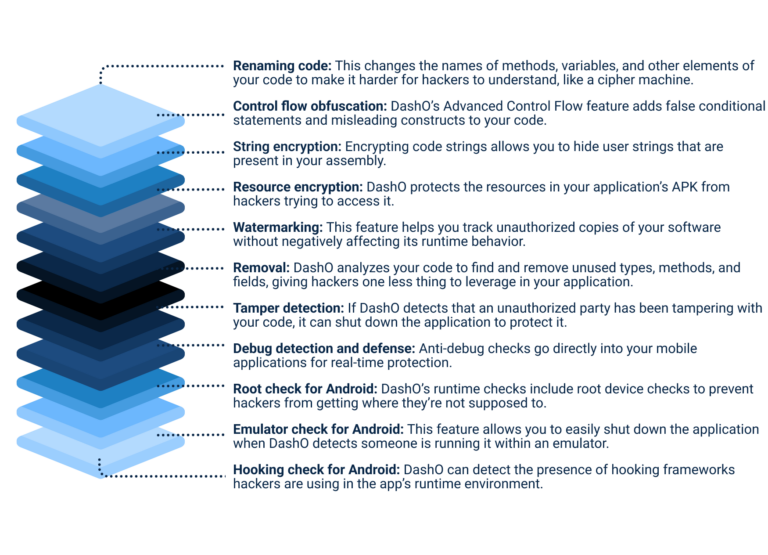
DashO offers professional-grade protection to add multiple layers of security measures to mobile applications, making it more challenging for hackers to successfully reverse engineer your app. In turn, this makes it harder for them to steal your intellectual property, compromise your users’ data, or harm your business.



A holistic approach to DevSecOps also requires static application security testing to find vulnerabilities in your source code. That’s where PreEmptive’s sister brand and partner in protection comes into play.
Kiuwan is a powerful end-to-end application security platform that combines SAST, SCA, and QA tools to help developers find and quickly remediate vulnerabilities in their source code. Together, these desktop and mobile app security tools safeguard your applications from development to deployment against hacks, data breaches, and attacks. Schedule a demo today to learn more about how you can use these two tools together to create a better app
Developers are constantly creating new apps for Android users. However, not everyone downloading your app has good intentions when they download it.
Using obfuscation tools is a preventative measure that keeps your application and its users safe from cybercrime.
Like any other type of mobile code, apps written for Android are at risk of reverse engineering attacks, especially if they don’t already have robust security features in place. Having application and Java security tools in place to regularly monitor your app for signs of hacking attempts can potentially save your brand thousands—or even millions—of dollars in damages, fines, and lawsuits from a data breach.
Yes! For the iOS versions of your applications, we also offer Defender for iOS. This program offers professional-grade app security and protection for iOS-based applications.
In addition to control flow and rename obfuscation features, Defender for iOS also includes jailbreak detection. This enables your team to identify and remediate when users have obtained elevated privileges that would allow them to introduce security vulnerabilities.
In addition to deploying DashO for your existing applications, it can also be helpful to implement it during all phases of the software development life cycle. Doing so allows your team to take a DevSecOps approach to building your application—in turn, making your entire app both higher quality and more secure.