ClickOnce is a popular way to deploy and keep applications up to date without a lot of hassle. These applications are downloaded to the end user’s machine after being published to the server, which means they can easily be decompiled and reverse engineered like other .NET applications.
Protecting an application that is deployed via ClickOnce is usually very complicated. After protection, the application and deployment manifests must be manually updated using the Mage tool. Signing of manifests and assembly files must be done manually, as well.
With Dotfuscator, we’ve worked to make this process much simpler.
In 4x versions, Dotfuscator accepted the ClickOnce .application as direct input. It would re-generate the obfuscated assemblies along with the updated .application package. The updated deployment manifest and protected binaries would then be copied to the ClickOnce deployment server to be downloaded by the end-user.
Starting with version 6, we’ve made this process even easier. We just have to integrate Dotfuscator into our application’s project file (.csproj, .vbproj).
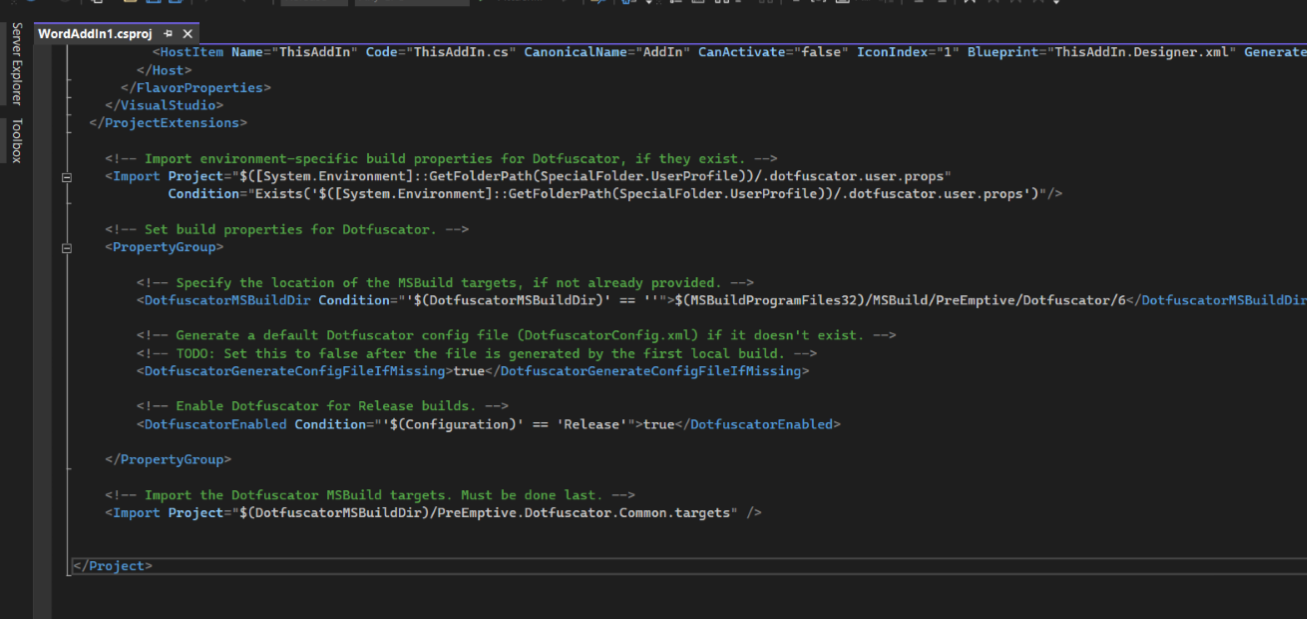
Doing so triggers Dotfuscator to run before packaging steps of our Release build. Protected binaries are then automatically packaged for deployment. No additional steps required.
We’ve worked with customers that deploy through ClickOnce, and also create an installer for offline installs. This process allows us to do both without any additional steps.
A simple ClickOnce project with Dotfuscator integration can be downloaded here. A release publish of this project generates obfuscated binaries. Double-clicking the .application manifest simulates a download and install of the ClickOnce application on the client’s machine.

If you have feedback on this topic or other topics you would like us to discuss in the Support Corner, please feel free to contact our Support Department.