PreEmptive Protection - Dotfuscator 4.33
User Guide
Getting Started
Understanding Protection
- Overview
- Additional Protections
- Library Mode
- Building and Debugging
- Identify Renaming Exclusions
- Advanced Topics
Understanding Obfuscation
Understanding Checks
Understanding Instrumentation
Using the GUI
- Overview
- Using the Standalone GUI
- Using the Visual Studio Integrated UI
- Renaming Editor
- Control Flow Editor
- String Encryption Editor
- Removal Editor
- Linking Editor
- Premark Editor
- Injection Editor
- Using the Graphical Rules Editing Interface
- Customer Feedback Options
- Decoding Obfuscated Stack Traces
- Using Lucidator
References
Using Lucidator
To translate complete stack traces, open a map file produced by Dotfuscator. Next, open Lucidator by clicking Tools > Decode Obfuscated Stack Traces... or by using the following commands in the command line:
| Options | Description |
|---|---|
/mapfile=<map file> |
specifies the map file (e.g.: /mapfile=map.xml) |
/stacktracefile=<stack trace file> |
specifies the file containing the stack trace (e.g.: /stacktracefile=stacktrace.txt) |
/c=<culture> |
set user interface language (requires appropriate language resources). Argument is the lowercase language code:(e.g.: /c=de, /c=ja, /c=zh-CHS) |
When the Lucidator window displays on your desktop, select the Translate Lines tab, and then paste the stack trace in the window. Click the Translate button.
The translated stack trace displays in the Translation Report section of the window.

Methods in obfuscated stack traces may be ambiguous due to the use of Overload Induction and Enhanced Overload Induction. Because there may be more than one matching unobfuscated method, Lucidator displays all the possibilities. To look up a specific type or method by name, click the Translate Specific Element tab:
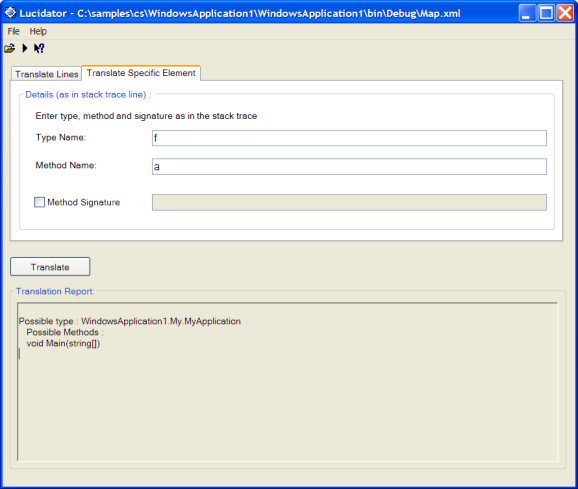
In this screen, enter the obfuscated names of the specific items you want to translate. For example, to translate an obfuscated type name, enter the obfuscated name in the Type Name: field and click Translate. Likewise, to translate an obfuscated method name, enter the obfuscated name in the Method Name: field and click Translate. You may optionally provide a signature by checking the Method Signature box and entering the signature in the adjacent text box.
Note: The signature must be as it appears in the stack trace.
Dotfuscator Version 4.33.0.6680. Copyright © 2017 PreEmptive Solutions, LLC