That was the title of yesterday’s congressional briefing organized by ACT | The App Association (in cooperation with the Congressional IP Caucus which is co-chaired by Rep. George Holding, Rep. Adam Smith, & Rep. Hakeem Jeffries).
As is often the case when presenting to different kind of audience (not software-centric), you’re forced to reorganize your thoughts – here are few that might be worth sharing.
Attendees were promised the following agenda:
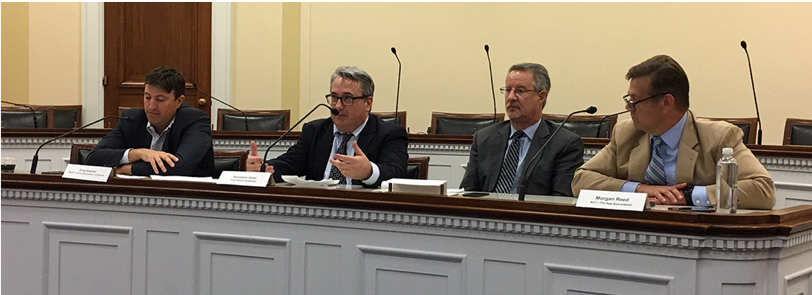
The panelists represented a nice cross-section of stakeholders.
First, I have to thank ACT (again) for their amazing work connecting software developers with their representatives (and vice versa) – and, more selfishly today, for inviting me to participate as a panelist (I always leave ACT events feeling maybe a little guilty hoping that I contributed at least as much as I took away).
The bad news is that every representative is away campaigning in their districts – but that was actually the good news – this meant that their staff (who have heavy influence over their boss’ final positions) were free to attend – and we did indeed have a full house – with lots of questions that went beyond the scheduled time slot.
The following summary covers just two of the topics raised and my responses (I don’t want to presume to quote anyone else). I think that the fact that these topics are front of mind on Capital Hill and this audience is extremely important all by itself.
As a developer of protection tools for software applications, can you tell us what your clients are experiencing in terms of piracy? (both consumer facing apps and enterprise software attacks)
My response: Consumer facing
Enterprise facing
So, pirates or hackers are not just ripping off content to redistribute it for a profit. Tell us more about why hackers are attacking your clients’ apps?
My response: We’ve seen a dramatic rise in hackers using apps as a means to get to the data that flows through those apps – examples include
As encryption has become more effectively deployed, hackers use developer tools like debuggers to access the data at the only time it isn’t encrypted – when it’s in use – in memory –
They use developer tools to see user data – but also tokens, passwords, and other sensitive data that can be used to elevate user privileges and execute unauthorized code as well.
In fact – from an engineering perspective – there is virtually no distinction between stealing content as a means to compromise systems, e.g. using a trusted brand to deliver a malicious payload versus compromising software or a device to steal valuable content like movies or games from a jailbroken Firestick.
So… the hacking breakthroughs for one criminal pattern (like watching illegal movies) can be equally useful to a multitude of other criminal activities – and – as such – are widely shared and valued by other classes of pirates, cyber-criminals, and nation-state actors.
There were many more questions (and answers) of course – if you’d like to learn more about this briefing and others like it – visit www.actonline.org and introduce yourself – if you have any comments or questions on the topics raised here – (or would like to learn about how PreEmptive Solutions is helping others), please do not hesitate to contact me directly.