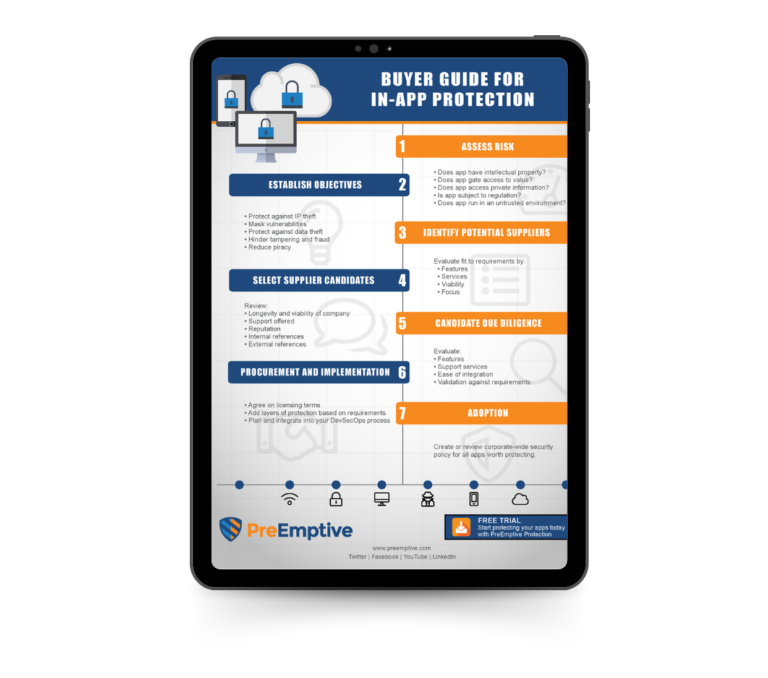
If the answer to these questions is yes, then read on…
Because data is created, accessed, and changed through applications, hardening and shielding your applications is a key component to protecting your data. Adding application protection to your secure software development lifecycle will make it more difficult for people and machines to exploit them.