| Transform | Description |
| DomainLock | Allows binding the code to a specific domain (or its subdomains). When the code running in the browser originates from a non-matching domain, it breaks with an error. |
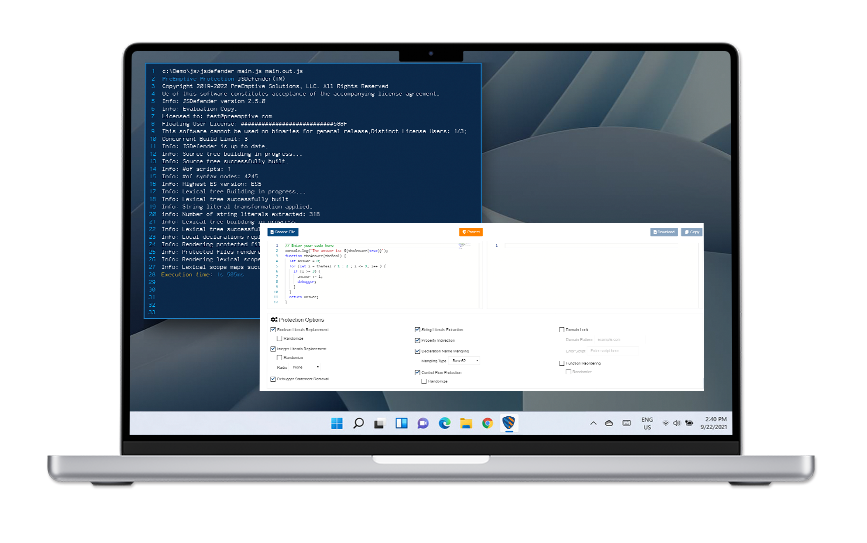
| BooleanLiterals | Transforms the false and true literals to other expressions that result in the same false and true values, respectively. |
| IntegerLiterals | Transforms integer literals to other (less obvious) expressions that result in the same value when evaluated. It can also transform all integer literals to a specific radix (binary, decimal, hexadecimal, or octal). |
| PropertyIndirection | Transforms direct property access to indirect property access. |
| StringLiterals | Extracts string literals into variables and initializes those variables from encoded string literals. Replaces the original string with the corresponding variables. |
| LocalDeclaration | Mangles the names of local declarations. |
| DebuggerRemoval | Removes information from production code that can help hackers inspect your code. |
| ControlFlow Protection | Obfuscates the program’s control flow by adding opaque predicates or dead code and flattening the control flow. |
| Function Reordering | Moves functions from their original locations to a new one in the same lexical scope. When the *randomize* option is turned on, it sets the new location randomly. |
| Tamper Detection | Wraps critical code with guarding functions, which check at runtime for modifications. Tampered code will not run correctly. |
| Date Lock | Injects code into the protected source, which tests if the current date is in a particular interval. If so, the code runs normally; otherwise, it can either exit or run a custom script. |
| Expression Sequence Obfuscation | Collects adjacent expression statements in the code and joins them into an expression sequence that is harder to understand. |
| Property Sparsing | Transforms object literal expression assignments into multiple assignment statements to make them harder to read. |
| Variable Grouping Protection | Separates variable declarations and initializations; it moves the declaration part to the end of the declaration scope. |